Identity Theft
Identity Theft
Phishing scams are on the rise. If you get a text claiming to be from CPB and are asked to provide your full card number, PIN number, or online banking credentials, contact our Customer Service Center immediately at 808-544-0500.
If you're looking for information about identity theft, you can visit the Hawaii Department of Commerce and Consumer Affairs website or the Federal Trade Commission's Identity Theft website.
Fraud
Fraud can come in many forms. It is important as a consumer to protect yourself to avoid becoming a victim. One of the most common types of fraud attempts is to steal your identity. Identity theft starts with the misuse of your personally identifiable information such as your name and Social Security number, credit card numbers, or other financial account information. For identity thieves, this information is priceless.
There are many ways to try and steal this information, which include but are not limited to the following:
- Dumpster Diving. Rummaging through trash looking for bills or other documents containing your personal information.
- Skimming. Stealing credit/debit card numbers by using a special information collection/storage device when processing your card information.
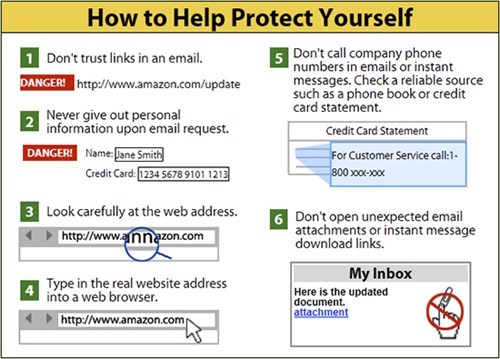
- Phishing. Acquiring information such as usernames, passwords and credit card details by masquerading as a trustworthy entity usually via email. The email often instructs users to enter details at a fake website that looks and feels like they are on the legitimate website. Communications purporting to be from popular social web sites, auction sites, online payment processors or IT administrators are commonly used to lure the unsuspecting public.
- Mail Theft. Stealing your mail from your mailbox hoping to find bank statements or payroll/social security checks mailed to your home.
FIGHT BACK AGAINST IDENTITY THEFT
DETER identity theft by safeguarding information
- Be careful of how you disclose private information, such as displaying your Social Security Number on checks.
- Shred documents such as credit cards, insurance & other financial statements before discarding.
DETECT suspicious activity by monitoring accounts
- Review transactions (online is best).
- Be alert for statements that don't arrive as expected.
- Ask for your free credit report every 12 months. Visit www.AnnualCreditReport.com or call 1-877-322-8228.
DEFEND against identity theft as soon as you suspect a problem
- Follow reporting procedures shown below to speed your recovery.
IDENTITY THEFT
Unauthorized Access to Your Personal/Private Information
If you know or suspect that an unauthorized party has your personal/private information, such as information relating to or which can be used to access your financial accounts, funds or assets, such as your bank, credit card, debit card, or investment account numbers or statements or any passwords or security codes, then you should take the following actions.
Notify the financial institution/company immediately.
Be vigilant over the next 24 months and promptly report to your financial institution/company any incidents of suspected identity theft.
Review your account statements and immediately report to your financial institution/company any suspicious activity or unauthorized transactions.
Consider placing a fraud alert on your consumer/credit report by contacting one of the three nationwide credit bureaus/reporting agencies: Equifax, 1-800-685-1111, www.equifax.com; Experian, 1-888-397-3742, www.experian.com; TransUnion, 1-888-909-8872, www.transunion.com. You only need to contact one of the credit bureaus, as each of them are required to notify the others. A fraud alert is free and can help notify your creditors and also make it harder for an identity thief to open accounts in your name.
Consider filing a police report.
Periodically obtain credit reports from each of the three nationwide credit bureaus/reporting agencies and have information relating to any fraudulent transactions deleted. You may obtain credit reports free of charge (once every 12 months, upon request) from www.annualcreditreport.com, or by calling 1-877-322-8228, or by completing an Annual Credit Report Request Form and mailing it to Annual Credit Report Request Service, P.O. Box 105281, Atlanta, Georgia 30348-5281.
For information on what additional steps you can take to protect yourself against identity theft please visit the Federal Trade Commission (FTC) website at www.identitytheft.gov. Report incidents of identity theft to the FTC at www.identitytheft.gov or by calling 1-877-438-4338.
To report a phising and/or fraud attempt, contact us
Protect Your Device.
Do not allow others access to your computer. You should not allow anyone to use your computer as such individual could gain access to your private and personal information, to your passwords, PINs and other security configurations, and to your applications and systems, which such individual could then use to steal your identity and steal from you and your financial accounts and funds through conducting banking, financial, and other transactions using your name and passwords. Fraudsters will commonly attempt to gain access to a victim’s computer under false pretenses such as helping the victim get a government payment or cash prize online or helping the victim with making a transaction or accessing an application. Fraudsters will use all modes of communication to contact victims, such as via phone, emails, websites, and text messages. Be extra careful before responding to sources you don’t know.
Protect Yourself from Fraudsters.
Fraudsters may impersonate Central Pacific Bank and try to get you to reveal your personal, bank account, and financial information so they can steal from you. If you are not certain that a call, email, text, letter or communication is from Central Pacific Bank, please verify by calling our Customer Service at (808) 544-0500. If you believe you inadvertently provided information to a fraudster, please contact us immediately. For further information regarding ways to avoid fraud and identity theft please visit the FTC website: https://www.consumer.ftc.gov/articles/0060-10-things-you-can-do-avoid-fraud.
Protect Yourself and Your Money from Online Criminals
- If you assist a criminal with money laundering you are committing a crime.
- Do not give money to or have financial dealings with someone you meet online or over the phone.
- Never agree to be a money mule for someone you meet online or over the phone.
- Never agree to open an account with or for someone you meet online or over the phone.
- Never respond to online ads or phone offers to earn quick and easy money by assisting with money transfers.
- Never agree to receive and send money for someone you meet online or over the phone.
- Never receive, deposit or cash checks from someone you meet online or over the phone.
- Never wire or send money to someone you meet online or over the phone.
- Never invest and send money to someone you meet online or over the phone.
- Never give your user name and password to anyone.
- Never give your personal or financial information to anyone.
- Use different user names and passwords for different applications.
- Change user names and passwords regularly.
- Never respond to emails from people you don’t know.
- Never open email attachments in emails from people you don’t know.
- Don’t be a victim.
- Don’t be an accomplice to a money crime.
Protect Yourself from an Online Dating Scam
Scammers know millions of people use online dating sites. They are there hiding behind fake profiles.
Signs of a scam
- Professes love quickly. Claims to be overseas for business or military service.
- Asks for money, and lures you off the dating site.
- Claims to need money - for emergencies, hospital bills, or travel. Plans to visit but can't because of an emergency.
Learn more about online dating scams.
Beware of Government Imposter Scams
Scammers will typically call, email, text or direct message consumers on social media, stating that they represent a government agency and that the consumer is in violation of some law and that immediate payment must be made to cure the violation, or, that the consumer is entitled to some benefit but must make an immediate payment to receive the benefit. In some scams, the scammers will ask for the consumer’s personal information or financial account information in order to use the consumer’s identity to obtain government benefits or loans or to steal the consumer’s funds from their financial accounts. Scammers often attempt to frighten and scare consumers into sending funds to avoid something bad happening, or to entice consumers into sending funds to get some benefit. See further information on government imposter scams, here.
How to Protect Yourself from Becoming a Money Mule
Criminals use money laundering techniques to conceal their identity, source, and destination of illicitly obtained money. To do this, they rely on often unsuspecting money mules to transfer proceeds from their crimes without being detected by law enforcement. Money mules are individuals who transfer illegally obtained money on behalf of others using bank accounts, wire transfers, money orders, or checks.
Learn more
Prevalent Social Engineering Scam
Consumers are receiving text messages from fraudsters alerting the consumer about a suspicious financial transaction. Upon receiving a response text declining the transaction from the consumer, the fraudster calls the consumer, pretending to be the fraud department of the financial institution. The fraudster gains access to the consumer’s online banking account by requesting the username and password, which the fraudster then uses to reset the password. Upon gaining access to the online account, the fraudster proceeds to transfer, withdraw and steal the consumers’ funds in the account. Be aware of other common scams here.
Consumers should protect their bank accounts by following these tips and best practices:
- Your financial institution will never call you to request information you received via text (SMS) or pressure you to reset your online banking log in password.
- Don’t trust caller ID; Caller ID may be modified to show your financial institution’s name.
- Don’t provide your online banking log in credentials, username, password, account number or personal information by email or text or phone call. Using their published phone number, reach out to your financial institution to confirm that the request is legitimate.
- Don’t give information over the phone if you receive a call stating that a transaction is canceled, even if the caller claims to be from your financial institution. Once again, contact your financial institution using a published phone number to inquire about the transaction.
- Don’t click on links in unsolicited emails or texts.
- Don’t give an unsolicited caller remote access to your computer.
See the latest news on how to protect yourself from identity theft and other scams.